SSH Radar:
Real-Time Attack Monitoring
A real-time monitoring and visualization platform that tracks failed SSH login attempts on a Linux server. Built after discovering thousands of brute-force login attempts from bots worldwide.
Why I Built This
It started when I opened port 22 on my Oracle Cloud server and discovered thousands of brute-force login attempts from bots worldwide. Instead of just blocking them, I decided to build a full pipeline to collect, enrich with geolocation data, and visualize these attacks in real time.
"Every 5 minutes, real attack data flows through the pipeline — parsed, geolocated, and visualized. It's not simulated. It's the internet trying to break in."
Key Features
Real-Time Live Feed
Failed login attempts replayed with a 5-minute delay, Web Audio API blip sounds, deduplication. Shows timestamp, username, IP, and location.
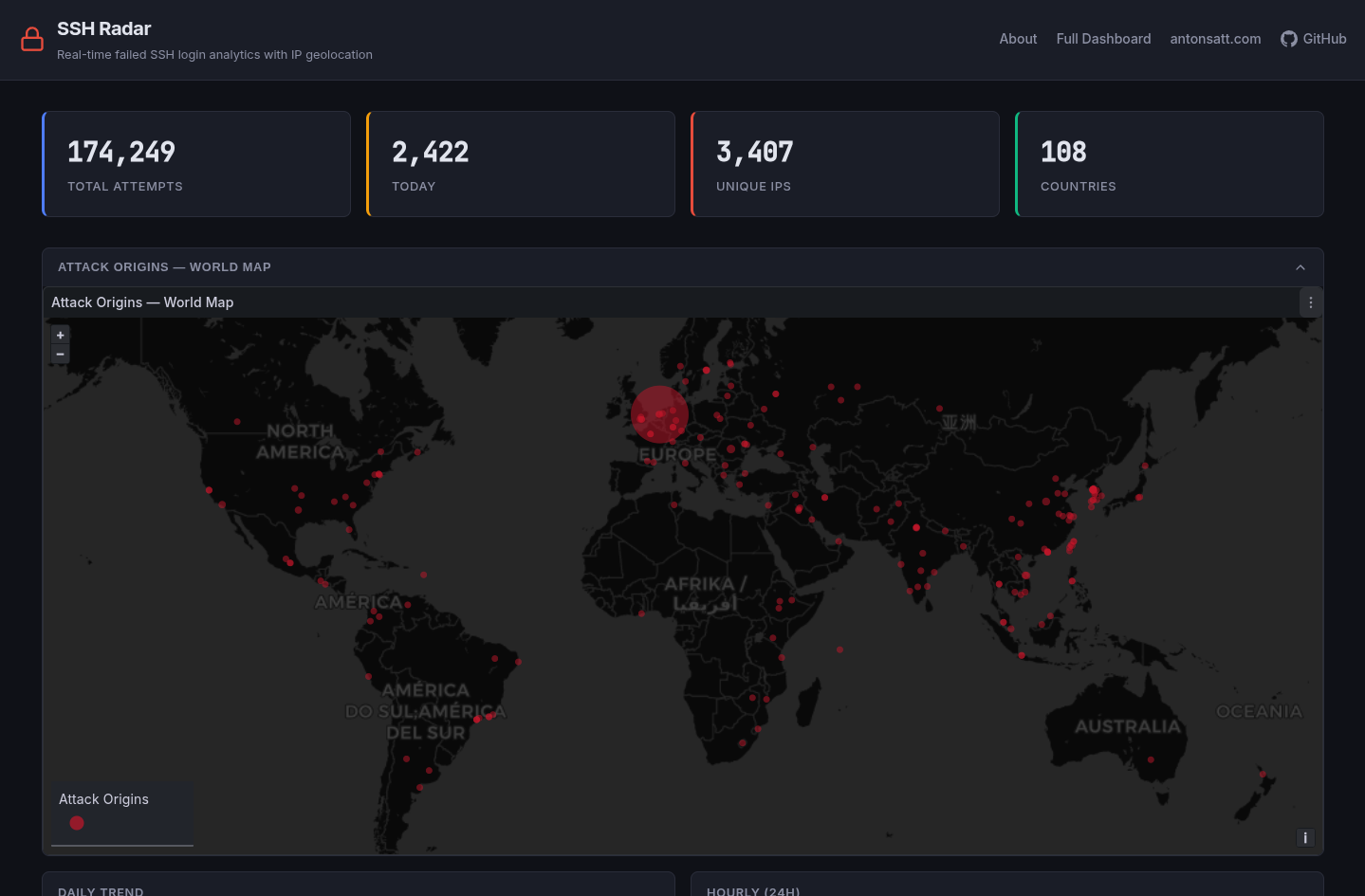
Stats Dashboard
5 live stat cards: Total Attempts, Today's Attempts, Unique IPs, Countries, and Days of Data — all auto-refreshing.
Top Targets Carousel
Scrolling display of the 10 most attacked usernames with attempt counts.
Embedded Grafana Panels
World map with attack markers, daily/hourly trend lines, top countries pie chart, top IPs/usernames bar charts.
Automated Pipeline
Host cron runs lastb every 5 minutes, Python parses and deduplicates, enriches IPs with geolocation, and bulk inserts to PostgreSQL.
45 Automated Tests
Parser tests, geolocation tests, and integration tests with temporary Docker PostgreSQL.
Architecture
Internet → HTTPS (Let's Encrypt)
→ nginx-proxy
→ Frontend (React SPA via Nginx) :80
→ Grafana :3000
→ PostgreSQL :5432 (localhost only)
Host cron (every 5 min):
lastb -F → Python parser → Geolocation enrichment → PostgreSQL
Tech Stack
Screenshots

Project Links
Project Details
Type
Personal Project
Status
Live & Running
Hosting
Oracle Cloud Free Tier
Stack
Python, PostgreSQL, Grafana, React, Docker
Data
Real brute-force attack data from production server
Tests
45 automated tests (pytest)
License
MIT